Cybercriminals have found a new way to compromise WordPress websites by exploiting the mu-plugins directory to inject malicious code.
This stealthy technique allows attackers to gain persistent remote access, redirect visitors to fraudulent websites, and replace legitimate site images with explicit content.
Understanding the Threat – What Are mu-Plugins?
The term mu-plugins stands for “must-use plugins,” which reside in a special WordPress directory (wp-content/mu-plugins). Unlike regular plugins, these are executed automatically by WordPress without needing activation via the admin dashboard.
Unfortunately, this feature makes the directory an attractive target for hackers, as mu-plugins are not visible in the standard WordPress interface, making them harder to detect.
According to cybersecurity experts at Sucuri, attackers exploit this hidden directory to implant malware, allowing them to manipulate websites without being easily noticed during routine security scans.
How Hackers Exploit mu-Plugins to Compromise WordPress Sites
Security researchers have identified three types of malicious PHP code inserted into the mu-plugins directory:
- Redirection Malware (
redirect.php)- This script forces site visitors to an external malicious website.
- It disguises itself as a legitimate browser update prompt, tricking users into downloading malware capable of stealing sensitive data or deploying additional cyber threats.
- The script smartly detects search engine crawlers and prevents them from seeing the redirection, ensuring that infected sites remain undetected for a longer period.
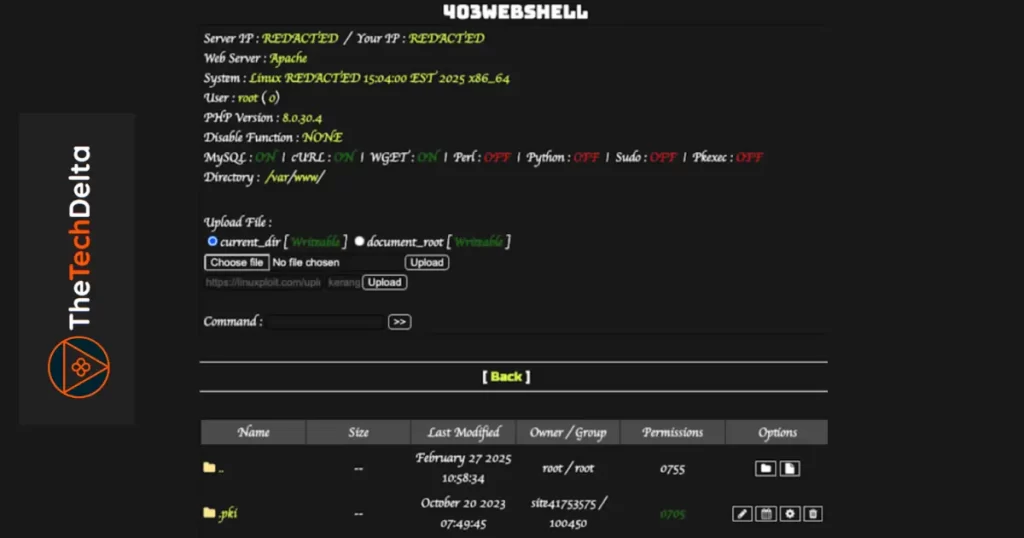
- Web Shell Backdoor (
index.php)- This backdoor enables attackers to execute arbitrary code remotely by fetching scripts hosted on platforms like GitHub.
- Cybercriminals use this to install additional payloads, steal user data, or take full control of the compromised site.
- Spam Injection & Image Hijacking (
custom-js-loader.php)- This script injects unwanted spam onto the infected website, likely to promote scams or manipulate SEO rankings.
- It replaces all images on the website with explicit content and hijacks outbound links, redirecting them to harmful destinations.
The Rising Trend of Hacked WordPress Sites Used for Cyber Attacks
Recent cybersecurity reports highlight that attackers are continuously exploiting vulnerable WordPress sites to launch large-scale cyber campaigns.
A common tactic, known as ClickFix, tricks users into executing malicious PowerShell commands under the guise of fake CAPTCHA verifications from services like Google reCAPTCHA or Cloudflare CAPTCHA.
This method is being used to distribute the Lumma Stealer malware, which harvests sensitive information from victims’ devices.
Additionally, compromised WordPress sites are being weaponized to:
- Deploy malicious JavaScript that redirects visitors to fraudulent third-party domains.
- Inject credit card skimmers to steal financial data from checkout pages.
The exact method of initial compromise remains uncertain, but cybersecurity experts suspect the usual culprits:
- Vulnerable Plugins and Themes – Outdated or poorly coded extensions provide easy entry points for attackers.
- Weak Admin Credentials – Stolen or easily guessable passwords allow unauthorized access.
- Server Misconfigurations – Poorly secured hosting environments make sites more susceptible to breaches.
Four Critical WordPress Vulnerabilities Exploited in 2024
According to a recent Patchstack report, threat actors have actively exploited multiple WordPress vulnerabilities this year, including:
- CVE-2024-27956 (CVSS Score: 9.9)
- An unauthenticated SQL execution vulnerability in the WordPress Automatic Plugin (used for AI content generation and auto-posting).
- An unauthenticated SQL execution vulnerability in the WordPress Automatic Plugin (used for AI content generation and auto-posting).
- CVE-2024-25600 (CVSS Score: 10.0)
- A remote code execution vulnerability in the Bricks theme, allowing hackers to take full control of affected websites.
- A remote code execution vulnerability in the Bricks theme, allowing hackers to take full control of affected websites.
- CVE-2024-8353 (CVSS Score: 10.0)
- A PHP object injection flaw in the GiveWP plugin, leading to remote code execution attacks.
- A PHP object injection flaw in the GiveWP plugin, leading to remote code execution attacks.
- CVE-2024-4345 (CVSS Score: 10.0)
- An arbitrary file upload vulnerability in the Startklar Elementor Addons, enabling attackers to install malware on vulnerable sites.
How to Protect Your WordPress Site from These Attacks
To mitigate these security threats, WordPress site owners should implement the following best practices:
- Regularly Update Plugins and Themes – Keep all extensions up to date to patch security vulnerabilities.
- Perform Frequent Security Audits – Regularly scan website files and databases for malicious code.
- Enforce Strong Authentication Measures – Use strong passwords, enable two-factor authentication (2FA), and limit login attempts.
- Deploy a Web Application Firewall (WAF) – Protect against malicious requests and prevent code injections.
- Monitor Website Activity – Keep an eye on unusual behavior, unauthorized file modifications, or unexpected traffic spikes.
Conclusion
Cybercriminals are becoming increasingly sophisticated, using hidden mu-plugins to gain persistent access to WordPress websites, inject spam, and hijack site images.
As attacks evolve, website owners must stay vigilant by strengthening security measures, updating plugins regularly, and monitoring for unusual activity.
By implementing robust cybersecurity practices, WordPress site administrators can protect their platforms from being exploited in these alarming and widespread attacks.



